DFS Leader DraftKings Vows to Get Even With DDoS Attackers

Just a couple of days after opening up an officially licensed sportsbook site in New Jersey last month, the fantasy football giant Draft Kings was subject to a DDoS attack.
On Aug. 7, an attempt was made to overload the company's servers, but it had negligible effects. On Aug. 8, however, the attack was renewed and succeeded in interrupting DraftKings' services for 26 minutes. What makes this incursion different from so many others is that Draft Kings has vowed to get to the bottom of this event and discover the true identity of the persons who instituted the attack.

Now you might think that this would be an easy thing to do and would merit the full cooperation of the authorities both nationally and abroad – but you would be wrong. Like anyone else who attempts to track down cyber-criminals, Draft Kings is totally on its own and has to spend its own hard-earned money to pursue the matter.
About DDoS

First, however, it may be a good idea to discuss what a DDoS attack is. DDoS stands for Distributed Denial of Service. The general idea is to flood a particular website with so many requests that it simply can't handle them all and essentially freezes up. People with legitimate interests in visiting the site find that things load so slowly (or not at all) that they give up and take their business elsewhere.
What makes DDoS possible is limited bandwidth. When you have a website, you also have a certain amount of bandwidth that services the traffic that wishes to visit your site. Think of it as a road that leads to your store. If you have a small store with few customers, you only need a one-lane gravel road to handle the traffic. If you have a super-size Walmart, you will need a much larger and nicer road to handle all of the people who are trying to get into and out of your operation.
Now, bandwidth costs money, so you only purchase as much as you think you will need (plus a little extra just to be sure). If you buy a superhighway-sized chunk of bandwidth but only have 5 visitors a month, you are losing a lot of money. Conversely, if you have 5 million visitors a month and only build a two-lane residential street, traffic is going to be murder. So what a DDoS attack does is dump several extra million visitors onto your bandwidth. Since none of these are legitimate customers, they are muscling your actual clientele out of the way.
Possible Motivations

Given that Draft Kings is entering the highly competitive field of sports betting, it may come as no surprise that they are resented by those who have already cut up the pie amongst themselves and are not anxious to settle for a smaller piece in the future. At least this is obviously what Draft Kings is thinking and, rather than tamely take it in the shorts, they have decided to hit back as hard as they can in the hopes of at least discouraging future attacks.
Of course, these attacks may not be anything more than a simple attempt at blackmail, i.e., a bid to extract money from DraftKings in exchange for promising to halt future DDoS activities. The point to keep in mind is that most people do not actively pursue the miscreants for very long. The road to detection is a very long one, and it is filled with countless layers of people who not only do not care but actively oppose anybody snooping around in their proprietary domains. Given the small likelihood of apprehending the attackers, plus the near impossibility of gaining any compensation for all the time, money, and effort spent in tracking them down, most targets give it up after making a few phone calls to the singularly unhelpful police and the equally unsympathetic domain registrars.
DraftKings Not Content to Do Nothing

Despite the difficulties involved in seeking redress for DDoS strikes, Draft Kings has persisted to the point of gaining a court order, granted Aug. 31 by the U.S. District Court for Massachusetts, that requires the hosting domains to cough up the IP addresses of at least some of the offenders. These initial IP addresses will, no doubt, be found to be merely the first layer of the onion. Going deeper most likely will reveal a large botnet filled with zombie addresses owned by people who have no idea that their computers have been enslaved in this manner.
Even this limited result would be a victory for the forces of law and order. It takes time to steal enough addresses to build a good-sized botnet. Having yours dismantled due to some industrious victim who refuses to just take their beating and move on is almost as bad as having your own identity uncovered.
Botnets make money for their masters. They can be used to blackmail people via a DDoS as is under discussion here. They can be used to mine cryptocurrencies, like Bitcoin. They can be used to launch gigantic spam advertising campaigns. Closing one down will really hurt the perpetrators and let them know how it feels to be on the other end of the stick.
Possible Consequences of DraftKings' Actions

By publicly admitting that they have been the victim of such an attack and launching a high-profile effort to get even, no matter what it costs, Draft Kings is pioneering a new deterrent-based approach to internet crime. Bad actors are no doubt going to feel safer in attacking some other target that doesn't have the money or the cojones to strike back.
In the high-profit world of online gambling, DDoS incidents have become almost a fact of life. Particularly on days when large-payout online poker tournaments are scheduled, these attacks create real havoc among both the gamers and their hosts. Worse, because of the highly interactive nature of such tournaments, it is essentially impossible to deny that these attacks are occurring. Too many people are direct witnesses to what is going on when poker sites are targeted by DDoS, which is extremely and unfairly damaging to the reputation of those who operate such games.
 Some of the Online Poker Organizations That Have Recently Come Under DDoS Attack
Some of the Online Poker Organizations That Have Recently Come Under DDoS AttackIf DraftKings should prove successful in discouraging further incursions against its internet infrastructure, this could have a spillover effect on to other online gaming firms. Once they have an example of retaliatory tactics that work, they'll be able to emulate DraftKings' strategy and discourage future DDoS incursions.
Other Possible Solutions

With regard to what else can be done to halt these insidious spoilers from having a seat at the table, the current answer is "not much." National and international organizations could (but won't) take a much more proactive role in shutting these criminals down. Given the interest that national spy agencies have in surveilling their own populations as well as foreigners, the data is almost undoubtedly already at their disposal – but they simply choose not to deploy those resources for this particular purpose.
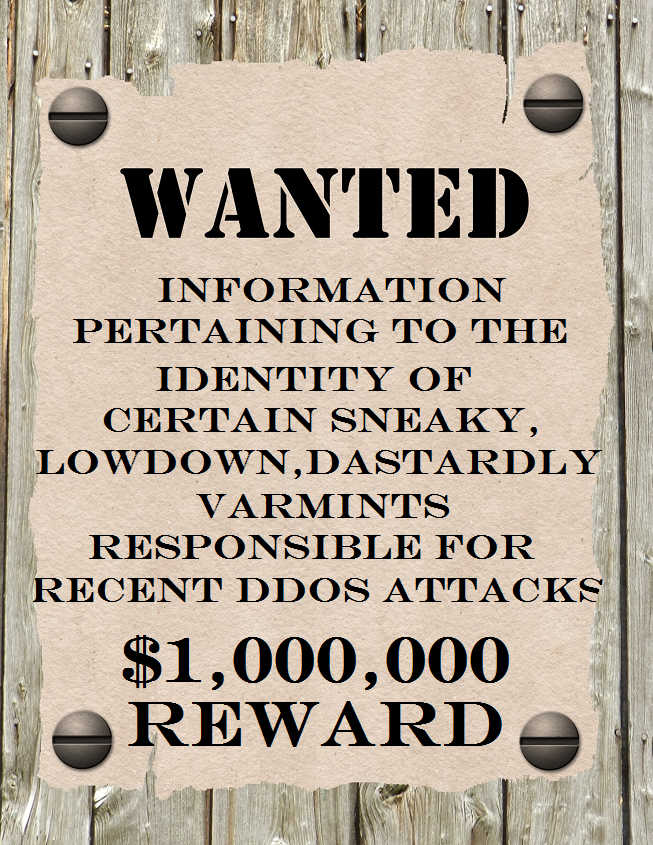
Perhaps it is time to return to the days of the Old West and resort to high-value rewards for the apprehension of anyone who does this sort of thing. Get the ineffective agencies out of the loop and let private bounty hunters drag these people out of the shadows. Nothing else is likely to create peace in the valley.